You could setup debugging and monitor all the traffic from the phone over a long period of time. Inspect it and confirm (or deny) your hypothesis.
This wouldn’t be conclusive since it would be pretty easy to just hide these payloads in some other traffic stream to a compromised node, which is a super common way cyberthreat command and control functions. If the user never initiates a connection to the host, the payloads just wait around so as not to generate suspicious traffic.
Obviously the threat model for advertising is a bit different, but there’s no reason someone trying to hide this functionality wouldn’t take similar steps.
Oh sure, you could be extra careful and attempt to detect any obfuscation or encrypted payloads that weren’t decrypted. Then there’s the concern that the malware watches for this behaviour and you’ll need to further modify the environment.
Wireshark won’t show you anything if it’s encrypted, other then a communication taking place. There’s nothing stopping them from batching or otherwise obfuscating things through all kinds of means.
It entirely depends on how you set it up and where in the transport pipeline you’re intercepting pockets from.
how do you circumvent the HTTPS encryption?
By combining with other methods for intercepting HTTPS traffic, typically involving installing certificates or modifying system configurations like configuring your browser or operating system to log secret keys.
To break down the process of the cert method :
- Device Trust: Install a trusted Root CA certificate (issued by you) on the Android device using Root permissions. This certificate tricks apps into trusting the proxy. Without Root level install the apps may reject the certificate as User Installed.
- Device Routes Traffic : Configure the rooted Android device to route its traffic to the proxy on the separate system. This can be done through proxy settings.
- Proxy Decryption : Configure the proxy to use the corresponding private key to decrypt the HTTPS traffic coming from your device, this key is generated when you created/issued the Root CA.
- Traffic Inspection : With the traffic decrypted, you can use Wireshark configured to the proxy to inspect the traffic.
- Proxy Re-encrypts and Forwards: After inspection, the proxy re-encrypts the traffic using a legitimate certificate and forwards it to the real website.
It would still be tedious to inspect every bit to ensure that a rogue service isn’t just tacking chunks of noise onto a legitimate data stream. I’d argue that it’s almost impossible to verify that every bit is legitimate unless you also control the host and know exactly what the traffic is supposed to look like.
by “the host” you mean the server?
With the traffic decrypted it should be possible to automate the inspection process to some degree, but obviously milage may vary.
Should the notification tell you when an app uses your mic when not inside the app?
Oh wait, it can’t if one bypasses the API.
They are, so, why bother?
You can’t prove a negative.
I can prove by evidence that there is no milk in this cup.

Yes but can you prove by evidence that there is no milk in my cup, if I won’t let you look inside?
Someone wants a glass of milk :-)
Who doesn’t?
༼ʘ̚ل͜ʘ̚༽ ( ͡° ͜ʖ ͡°)
Proving the negative or positive would be equally hard then .
Yes, but an absence of a proof of the positive is itself not proof of the negative, so if we’re in the unprovable unknown, we’re still back at the point that you can’t prove a negative.
Well, if the conditions are such that the positive would be absolutely certain to leave evidence, then the lack of said evidence is good enough. Like, I say it’s not snowing where I live. Absolutely nobody in my town sees so much as a single snowflake. Also, it’s 72° out. Haven’t I proven to a reasonable degree that it’s not snowing where I live?
we’re still back at the point that you can’t prove a negative.
We were never at the point that you can’t prove a negative. That’s dumb & wrong.
A woman menstruating proves negative on pregnancy.
The existence of the largest prime was disproven thousands of years ago.
If you enumerate each particle in the cup and verify that it is not a milk particle, yes.
(Milk is a complex colloid of multiple compounds, so good luck with that.)
That’s such a widely used concept and it’s erroneous. You can’t ALWAYS prove a negative. But if you’re able to prove a mutually exclusive positive to the negative condition, then you’ve proven it. For example, proving it is daytime where I’m standing also proves it is not nighttime where I’m standing.
There are circumstances where a negative cannot be practically proven, or without an absurd amount of work. But all you really need to do is empirically demonstrate the negative is the likeliest reasonable scenario and that’s usually good enough, except to someone obstinately trying to stay with their position and therefore demands absolute unequivocal proof - which is a rarity entirely.
You can’t prove a universal negative.
You can prove specific negatives by providing counter evidence. Thing like “I am not a woman” by proving “I am a man”.
That depends on how conclusive you need your proof to be.
For example, you could run your phone software in an emulator and prove that your emulated microphone isn’t being accessed except when it should, because all attempts to access hardware are provided by your emulator. You would simply detect if this happens.
You could debug the kernel on device to detect request to access the microphone hardware and correlate this data with user activities to show that it’s quite unlikely you’re being monitored.
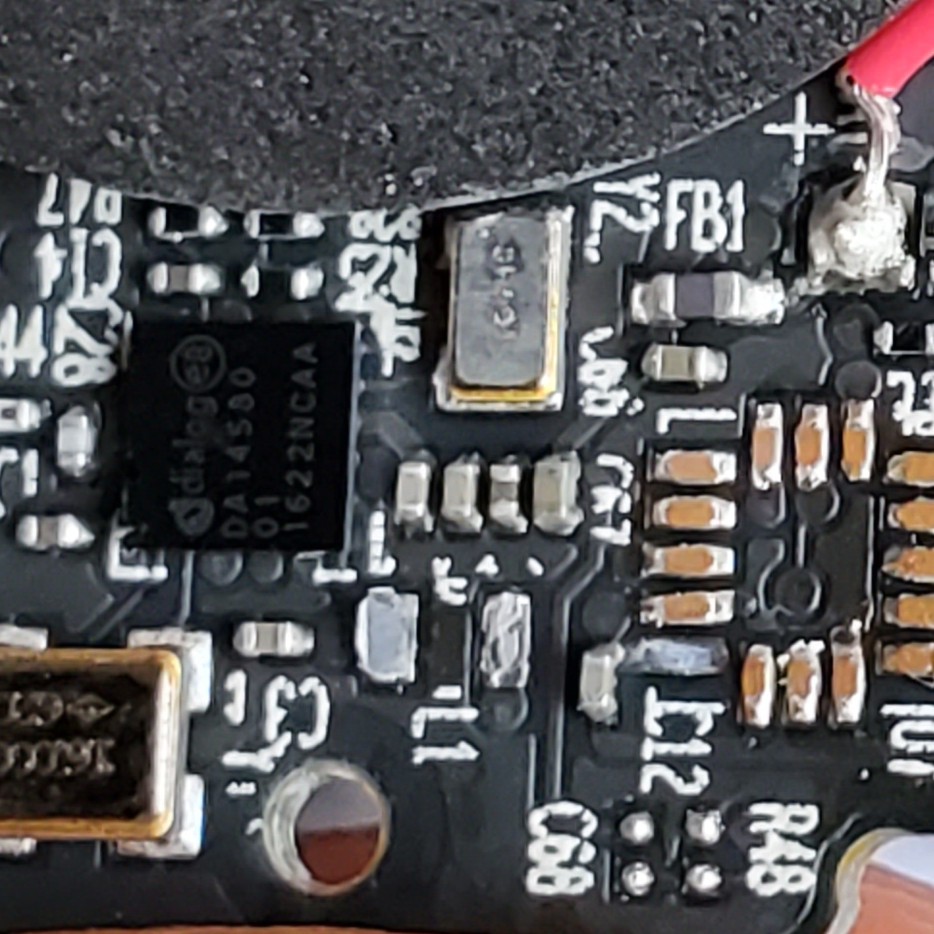
Perhaps you could insert physical probes into a real physical device to detect whether the application processor wakes up to service that data when you are speaking. If it doesn’t wake up, then you can reasonably argue that the data must not be getting stored or processed.
In general, irrefutable proof will be difficult to acquire. As far as we know, most phones don’t listen to the microphone and record audio while the screen is locked. They have a coprocessor that does this but it wouldn’t have the memory to record more than a second or two and is used mainly for hotword detection.
Put your phone in a Faraday bag for an extended period of time, then check what kind of ads you get.